New vulnerabilities and risks to the accuracy, timeliness, and business value of enterprise data are multiplying rapidly. This is largely because enterprise deployments of generative AI and other low-code/no-code technologies are growing explosively, often with little or no oversight by IT. The resulting transformations require new risk management approaches, including replacing traditional informational and operational silos with active, continuous collaboration.
Gartner estimates that by 2024, at least 80 percent of those building applications with low-code/no-code technologies will come from departments outside of IT. This compares with 60 percent of such users in 2021. However, this robust growth presents significant risk management challenges, as many of these deployments also take place without being vetted by enterprise policies for data protection and security.
The situation is intensifying with the growing adoption of generative AI, the latest high-profile low-code/no-code technology. Generative AI tools are already generating conversational answers to questions, graphics, music, and even complete marketing campaigns and software programs. And AWS has announced a new suite of tools intended to further “democratize” access to the power of generative AI.
Gartner predicts that by 2027, at least half of all investments in low-code/no-code technologies will focus on what the firm calls “packaged business capabilities,” or PBCs. However, this compares with only 5 percent of those investments used to create PBCs in 2021. PBCs are key elements of what Gartner calls “composable businesses,” digital enterprises that can adapt and reconfigure themselves as needed in response to market shifts or new business goals.
All of this means the growth of low-code/no-code technologies is likely to continue indefinitely and that those technologies will continue to gain new features. This means strategies and tactics for risk management must evolve almost continuously to keep pace with the data and resources being protected.
How Risk Management Must Change
At many enterprises, a chief risk officer (CRO) oversees risk management efforts. However, not all CRO roles are created equal. For example, some focus primarily or exclusively on financial or operational risk. But that leaves an important question unanswered: who is mainly responsible for protecting the data that drives the business?
Depending on the company, it could be a chief data officer (CDO), a chief security officer (CSO), a chief information security officer (CISO), or a chief information officer (CIO). Of course, it could also be someone who reports to one of these roles or even no one at all. And at some companies, a chief digital officer (a second CDO) is responsible for driving digital transformation, which includes at least partial responsibility for data trustworthiness.
Whatever specific roles and titles exist at your organization, the specifics of each role must be reevaluated given the changes being fomented by low-code/no-code technologies. This is because effective risk management will require cross-functional collaborations, some or all of which may be new to your organization or its leaders. For example, guardrails to protect enterprise data may be created by IT. Still, they must be vetted by HR and Legal to ensure the protection of both data and personal information and privacy. In addition, requirements for compliance with relevant laws, regulations, and best practices must also inform those guardrails.
What You Need To Do Now
Foster collaboration. At many organizations, those in roles directly related to risk management often operate in silos, sharing information or collaborating only when required or commanded to do so. Strategies and policies must be implemented or modified as needed to change this. No individual person or department can deliver effective risk management in isolation. And while executive leadership support can be valuable here, edicts “from above” will not make collaboration happen. Depending on the organization, new collaboration technologies, meeting and reporting policies, and other operational changes must all be looked at as potential enablers of the collaboration needed to deliver effective risk management.
Create a collaborative, risk-averse culture. In 2022, The Hackett Group published a research note entitled “Thriving in the Emerging Hybrid Workplace.” For that note, The Hackett Group asked hundreds of respondents across multiple business departments to cite the one change they saw as most likely to improve connections among colleagues and with the organization. The top five categories cited by respondents are shown in the figure below.
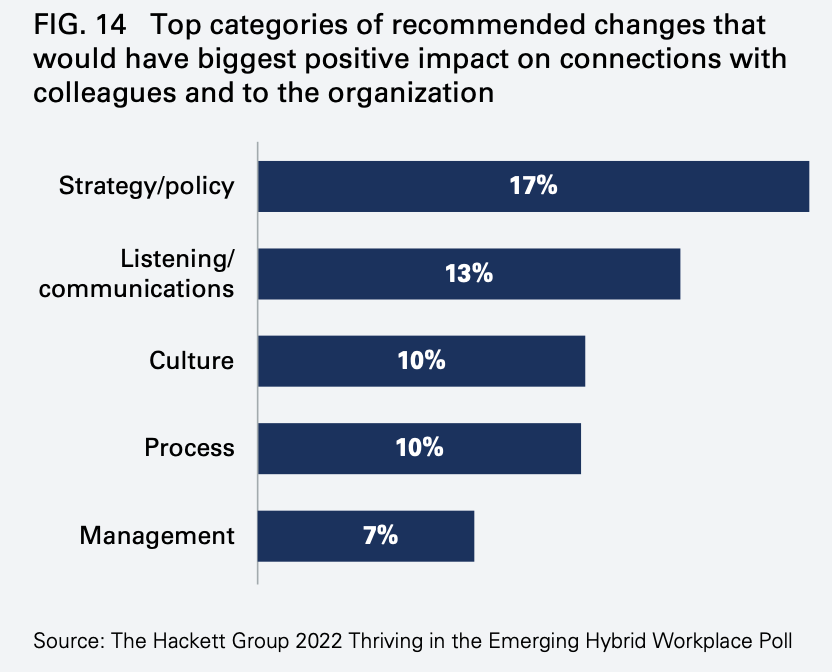
Low-code/no-code technologies are already proving to be at least as disruptive to the enterprise status quo as the rise of hybrid workstyles. Strategy and policy, listening and communicating, and building a shared culture focused on risk mitigation are as essential to achieving the level of collaboration your enterprise needs as they are to deal with hybrid work.
Automate everything. Your organization cannot manage or mitigate the risks associated with low-code/no-code technologies unless it knows everything about those deployments and the data they consume, manipulate and produce. Risk management leaders and their teams must ensure technologies and processes are in place that automate the collection and reporting of this information as much as possible. Manual processes simply cannot keep pace with the rate of change instigated by low-code/no-code adoption.
How Incisive Can Help
Incisive Software is focused on helping organizations build a strong foundation for success based on accurate and trustworthy data, a challenge exacerbated by the new and growing risks spawned by generative AI and other low-code/no-code technologies. Incisive offers Incisive Analytics Essentials, a solution that enables you to gain managerial control over generative AI and other low-code/no-code deployments while making them available to authorized users. The Concourse platform, the heart of the Incisive solution, provides consolidated, comprehensive abilities to know what you have and what changes and effectively manage, protect, and trust your business-critical data across your entire enterprise.
To learn more about Incisive Analytics Essentials or to arrange a demo or free trial, visit https://www.incisive.com, email [email protected], or call 408-660-3090.